Information Security Risk Assessment Questionnaire
Identifying and Mitigating InfoSec Vulnerabilities
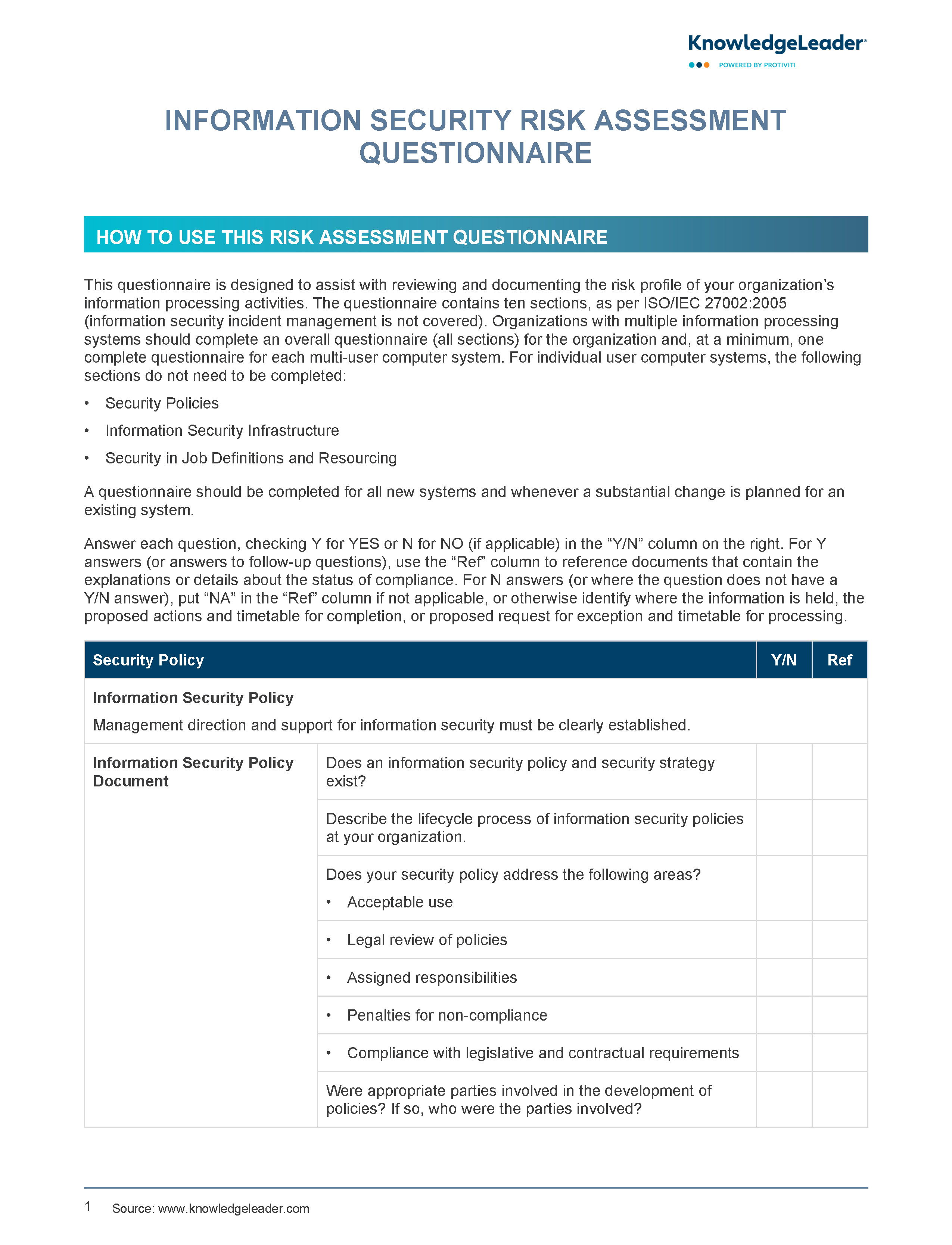
Organizations can use this IT risk assessment questionnaire to review and document the risk profile of their information processing activities.
Sample questions include: Has a forum been established to oversee and represent information security? If so, describe its governance/meeting schedule/structure. Has a process been established to coordinate the implementation of information security measures? If so, describe the process. Are security awareness programs in place? If so, describe the programs. (They should ensure that employees understand ethical and unethical uses of information and technology.) Are responsibilities for the accomplishment of information security requirements clearly defined? If so, how are these responsibilities assigned?